NOTICE: Infinity N5.2 and N5 FAQ 0.0.0
The wiki has been updated to include the N5.2 changes and the v0.0.0 FAQ.
List of wiki pages updated in N5.2.
Difference between revisions of "Quantronic Combat (Hacking)"
| Line 35: | Line 35: | ||
{{important-end}} | {{important-end}} | ||
| + | |||
| + | {{greybox-start | Example of Supportware Use and Cancellation }} | ||
| + | During their Active Turn, a Player that has two Troopers with EVO Hacking Devices on the table, declares Fairy Dust with one of them and chooses REMs as the Troop Type that will benefit from this Supportware. | ||
| + | |||
| + | For tactical reasons, they decide to spend the last Order on the other Trooper with an EVO Hacking Device to declare Enhanced Reaction on a REM located in the vanguard. | ||
| + | |||
| + | By designating a REM that was already benefitting from Fairy Dust, the new Supportware Program deactivates the Fairy Dust Program and the corresponding Token is removed from the table. | ||
| + | {{greybox-end}} | ||
== Firewall == | == Firewall == | ||
Revision as of 14:46, 15 September 2020
Combat Module Intro || Damage | Saving Rolls | Wounds and Structure | Unconscious | Dead | Guts Rolls || Ballistic Skills | BS Attack | Template Weapons and Equipment | Direct Template Weapons | Impact Template Weapons | Ranged Weapon Profile | Speculative Attack | Intuitive Attack || Close Combat | CC Attack | Engaged State | Melee Weapon Profile || Quantronic Combat (Hacking)
In Infinity, infowar and cyberwarfare tasks, defined as Hacking, are shouldered by the Hackers, specialized Troopers who can use the different Hacking Programs which define quantronic combat.
According to their nature, Hacking Programs allow the Hacker to act in an aggressive or defensive manner, support other Troopers, interact with scenery, etc.
When making your Army Lists in Infinity Army, a summary of the Hacking Programs will be included, in the same way that a summary of your Troopers’ weapons is included.
Hacker
See Hacker Special Skill
Upgrade Programs (UPGRADE)
Custom-made software tailored to the style and preference of specific infowar operatives. If available, they will be listed in the Unit Profile, in round brackets next to the name of the Hacker or the Device.
Supportware Programs
These are programs of extended duration which are mainly designed to support allied Troopers on the battlefield by granting them bonuses to improve their combat capabilities. Likewise, they may also be designed to hinder enemy Troopers, applying negative MODs to them.
- A Trooper can benefit from the effects of only one Program with the Supportware Label at a time.
- Each Hacker can only sustain one active Supportware Program at a time.
- A Hacker can cancel an active Supportware Program by declaring another Program and expending the corresponding Order or ARO.
- A Supportware Program is automatically cancelled if the Trooper or Troop Type targeted by the Supportware is targeted by a new Supportware Program, or if the Hacker running the Program enters Isolated State or any Null States.
During their Active Turn, a Player that has two Troopers with EVO Hacking Devices on the table, declares Fairy Dust with one of them and chooses REMs as the Troop Type that will benefit from this Supportware.
For tactical reasons, they decide to spend the last Order on the other Trooper with an EVO Hacking Device to declare Enhanced Reaction on a REM located in the vanguard.
By designating a REM that was already benefitting from Fairy Dust, the new Supportware Program deactivates the Fairy Dust Program and the corresponding Token is removed from the table.
Firewall
See Firewall
Hacking Devices and Hacking Programs: Characteristics
Hacking Devices and Hacking Programs have the following characteristics:
- They act in the user's Hacking Area.
- They do not require LoF to act, unless the Hacking Program's own description states otherwise.
- Only Troopers or Peripherals in Model form may be targeted by Hacking Programs.
- They benefit, if applicable, from the target's Targeted State.
Hacking Area
This term refers to the Area of Effect of Hacking Programs. In Infinity CodeOne a Hacker's Hacking Area matches their Zone of Control.
This term refers to the Area of Effect of Hacking Programs. In Infinity N4 a Hacker’s Hacking Area matches their Zone of Control, and the Zone of Control of Repeaters and Deployable Repeaters of either the Player or their Allies.
In addition, if a Hacker is within the Zone of Control of an Enemy Repeater or Deployable Repeater, their Hacking Area includes all Enemy Hackers on the game table.
Repeaters and Deployable Repeaters
See Repeaters, Deployable Repeaters
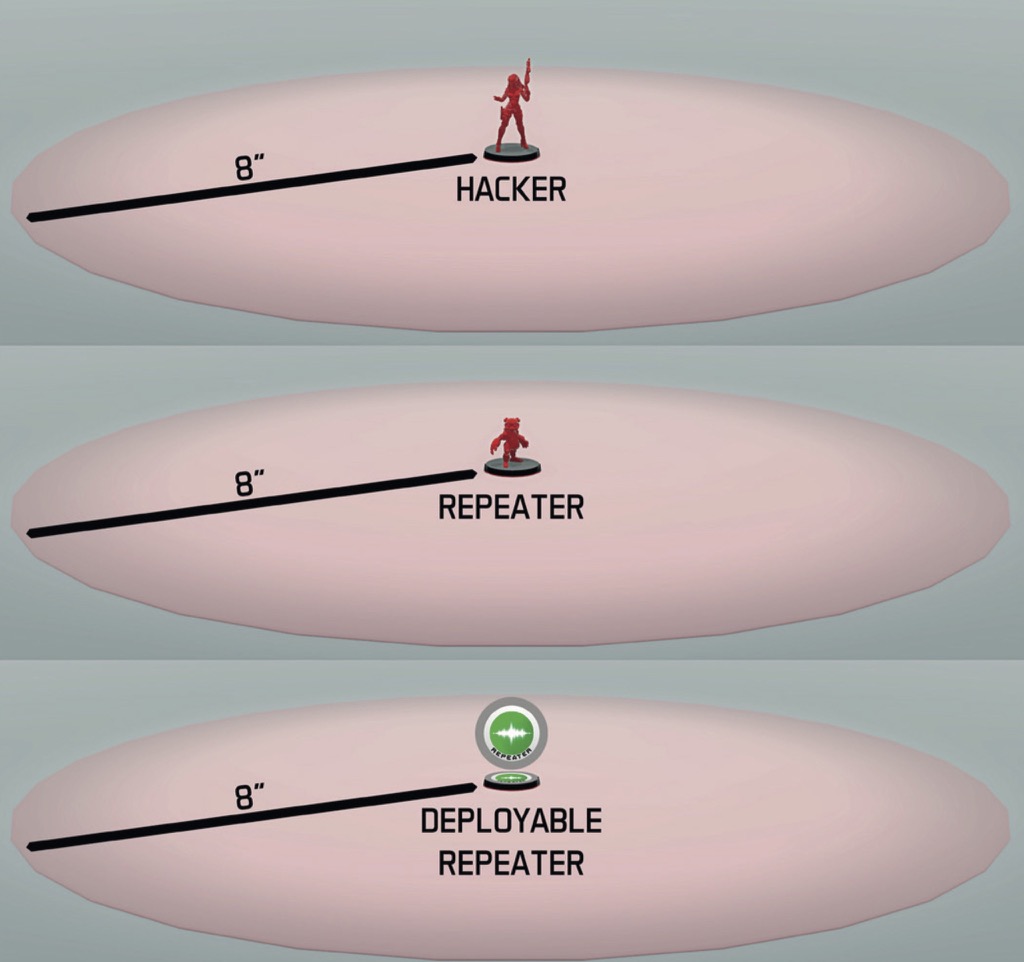
The Hacker may use their Hacking Programs in the area that includes the Zone of Control of the Repeater, the Deployable Repeater and their own Zone of Control.
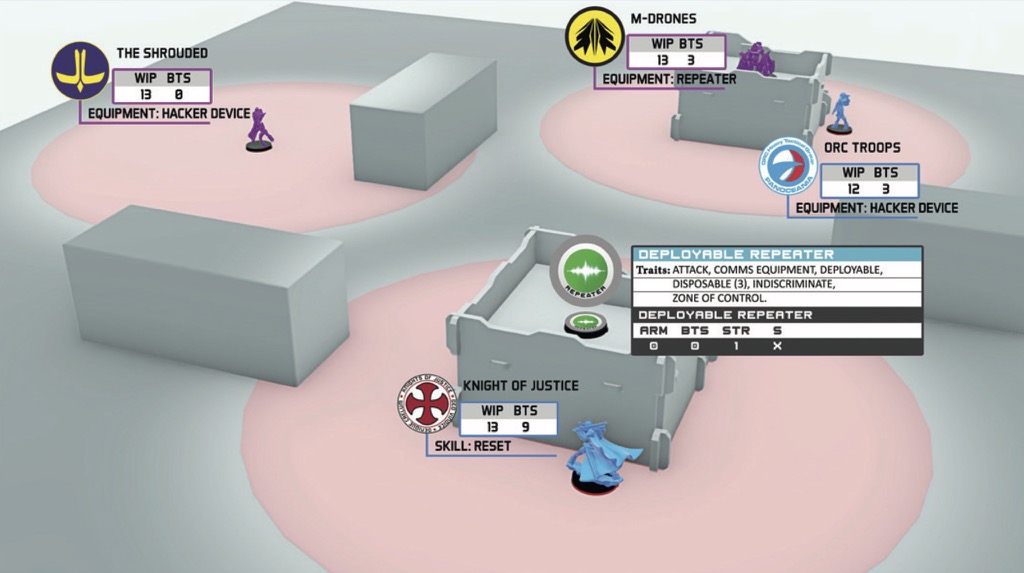
During his Active Turn, the Shrouded Hacker decides to declare Idle as the first Short Skill of the Order. As shown in the picture, he is outside his enemies LoF, but since he is a Hacker, he can use the Deployable Repeater, and the M-Drone Trooper (who carries the Repeater piece of Equipment), to increase his Hacking Area, allowing him to act from his current position.
Therefore, since both the Knight of Justice and the Orc Trooper Hacker are clearly within the Hacking Area of the Shrouded Hacker, they each declare their AROs.
The Knight of Justice declares Reset as their ARO and the Orc Hacker declares Oblivion.
The second Skill of the Shrouded Hacker is Carbonite, dividing his B2 between the Knight of Justice and the Orc Hacker.
During the Resolution of the Order, it is verified that both the Knight of Justice and the Orc Hacker are within the Hacking Area of the Shrouded Hacker.
The following Face to Face Rolls occur:
- Reset by the Knight of Justice vs Carbonite from the Shrouded.
- No Modifiers (MOD).
- Oblivion from the Orc Hacker vs Carbonite from the Shrouded.
- Orc Hacker MODs:
- -3 Firewall MOD for using an Enemy Repeater.
- Shrouded MODs:
- If a Saving Roll is required, the Attack Damage of Oblivion will suffer a -3 MOD from the Firewall.
- Orc Hacker MODs:
Hacking Programs Chart
Hacking Devices
See Hacking Devices
Example
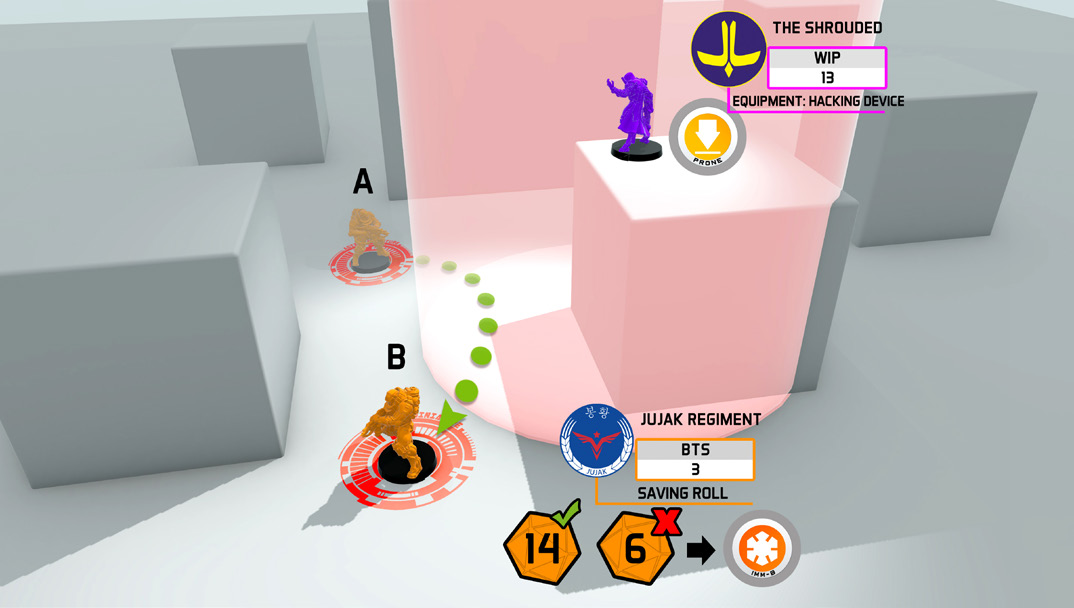
Step 1:
The Active Player declares Move with their Jujak from point A to B.
The Reactive Player declares the use of the Carbonite Hacking Program with their Shrouded Hacker.
Facing the possibility that the Jujak had passed within the Hacker’s ZoC, the Active Player declares Reset. They do not declare BS Attack to face the Hacker because it is clear that during their entire path they lack LoF to the Shrouded Hacker.
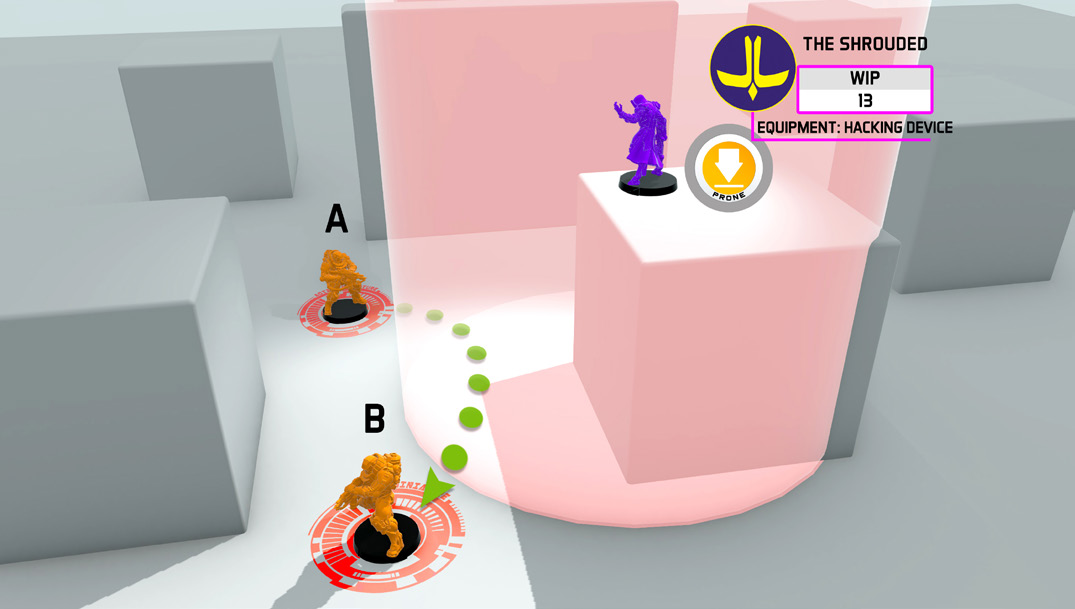
Step 2:
It is determined that, during their Movement, the Jujak indeed entered the Hacker’s ZoC and the Face to Face Rolls are performed.
Face to Face Roll:
Active Player, Reset (WIP Roll, in this case there are no MODs to be applied): 1 d20 with Success Value (SV) = 13.
Reactive Player, Carbonite (WIP Roll, in this case there are no MODs to be applied): 1 d20 with SV = 13.
They both succeed, but the 7 cancels the 3.
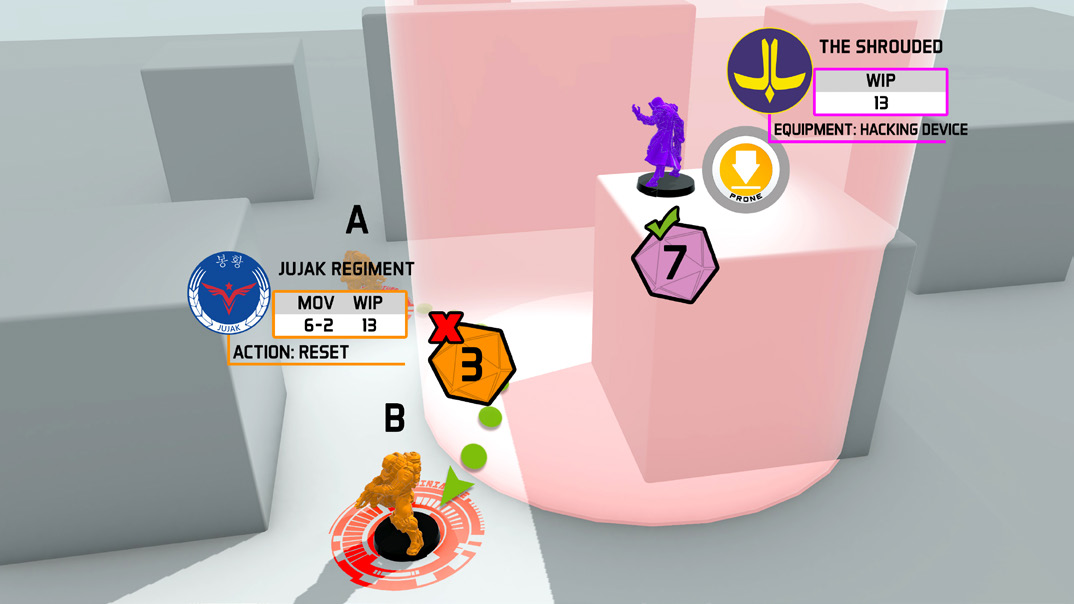
Step 3:
Therefore, after the Shrouded Hacker won the Face to Face Roll, the Jujak must perform 2 Saving Rolls due to the DA Ammunition against Damage 13.
Attack Damage = 10 (13 - 3 for BTS).
Due to the 6, the Jujak places an Immobilized-B Token next to him.
Combat Module Intro || Damage | Saving Rolls | Wounds and Structure | Unconscious | Dead | Guts Rolls || Ballistic Skills | BS Attack | Template Weapons and Equipment | Direct Template Weapons | Impact Template Weapons | Ranged Weapon Profile | Speculative Attack | Intuitive Attack || Close Combat | CC Attack | Engaged State | Melee Weapon Profile || Quantronic Combat (Hacking)